Threat Landscape stories - Page 57

Check Point unveils 'revolutionary' security protection
Mon, 3rd Mar 2014
#
cybersecurity
#
sdp
#
check point software
Check Point launches Software-defined Protection, a 'revolutionary' security solution for evolving IT threats, promising agility and robust defense.

Sun not yet set on Microsoft's Windows XP support threat
Sat, 18th Jan 2014
#
cybersecurity
#
microsoft
#
windows
Microsoft has extended support for Windows XP until July, but has stressed that it is not a supported operating system.

WatchGuard: Top 8 security predictions for 2014
Fri, 20th Dec 2013
#
firewalls
#
ddos
#
network infrastructure
Could a Hollywood hack come true? Will there be a US Healthcare.gov data breach? Should you expect CryptoLocker clones?.

Project 2020: Anticipating our cyber future to keep the bad guys at bay
Fri, 1st Nov 2013
#
cybersecurity
#
healthtech
#
trend micro
Picture the scene: it's the end of the decade. You live in a world where technology has become even more embedded into the fabric of society than it is today.

Cyber-attacks: 5 things companies should know
Fri, 17th May 2013
#
physical security
#
cybersecurity
#
hackers
Businesses are increasingly prey to sophisticated cyber-attacks targeting intellectual property, reveals a new guide by ISACA and experts at Ernst and Young.

Preparing for the Big Data revolution
Fri, 18th Jan 2013
#
data analytics
#
martech
#
planning
Security leaders urge organisations to prepare for how Big Date will transform security approaches and technologies by 2015.

F5 goes global with channel partner offering
Fri, 21st Dec 2012
#
cloud services
#
f5 networks
#
unity
Offered through the UNITY partner program, new security accreditation will increase understanding of F5's security offerings to drive revenue.

Threats? Manage with tech and policy.
Thu, 1st Nov 2012
#
data protection
#
dr
#
encryption
Whether a small business or an enterprise, when business information is on the line the organisation is at risk.

SonicWall tackles BYOD at Auckland event this Thursday
Tue, 6th Mar 2012
#
byod
#
sonicwall
#
mobility
SonicWall invites ICT managers to discuss BYOD and security trends at its Auckland seminar this Thursday. Key insights from industry expert Florian Malecki.

Proceed with caution
Fri, 1st Oct 2010
#
malware
#
cybersecurity
#
symantec
Mobile computing, social media and cloud top the security threat list for C-level executives and IT security professionals.

Sasfis Botnet variants multiplying according to latest Fortinet report
Tue, 3rd Aug 2010
#
firewalls
#
network infrastructure
#
network security
Fortinet report reveals a surge in Sasfis botnet variants, evolving to spam users with fake invoices and Facebook links.

Fortinet June Threat Landscape Report Shows New Variations of Sasfis Botnet
Thu, 1st Jul 2010
#
firewalls
#
network infrastructure
#
network security
Fortinet reveals new Sasfis botnet variations, escalating cyber threats in their June report, showcasing the evolving malware landscape.
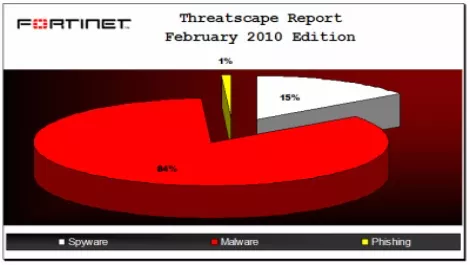
February's biggest IT threats named
Wed, 10th Mar 2010
#
firewalls
#
network infrastructure
#
network security
Fortinet reveals February's top IT hazards, with ransomware leading amid a surge in spam campaigns, showcasing the evolving cyber threat landscape.

Unite to secure!
Tue, 1st Dec 2009
#
malware
#
cybersecurity
#
management
As threats become more sophisticated, enterprises must shift from scattered, costly security measures to unified solutions for comprehensive protection.

Scareware dominates October threats
Tue, 10th Nov 2009
#
firewalls
#
network infrastructure
#
network security
According to the latest Fortinet report, scareware tactics dominated the October threat landscape and were four times more prominent than in September.

Microsoft makes waves with free AV
Thu, 1st Oct 2009
#
microsoft
#
chillisoft
#
distributors
Microsoft's launch of the free Security Essentials stirs the pot as Symantec criticises its effectiveness against modern threats.

Mac Musings from ESET
Wed, 22nd Apr 2009
#
apple
#
chillisoft
#
distributors
New revelations from ESET highlight how Macs are not immune to cyberattacks, challenging the myth of their invulnerability.