Cybersecurity strategy stories - Page 5

Ping Identity acquires Singular Key, extends no-code functionality
Thu, 30th Sep 2021
#
malware
#
devops
#
it automation
Ping Identity has acquired no-code identity specialist Singular Key to streamline integration of identity services.

Traditional solutions fail to secure organisations against today's malware
Tue, 29th Jun 2021
#
malware
#
firewalls
#
network infrastructure
Traditional anti-malware solutions miss nearly 75% of threats, according to new research from WatchGuard Technologies.

Companies not utilising threat hunters correctly – study
Tue, 17th Dec 2019
#
advanced persistent threat protection
#
cyber threat
#
study
ThreatQuotient study reveals confusion over the role of threat hunters, with many teams focusing on reactive processes.

75% of DevOps professionals say certificate issuance policies slow them down
Mon, 16th Dec 2019
#
devops
#
apm
#
software development
Less than half of DevOps professionals believe developers always request certificates that serve as machine identities through authorised channels.

Business security performance impacting bottom line - Thycotic
Mon, 2nd Dec 2019
#
pam
#
apm
#
software development
When cybersecurity teams do not meet their targets, it impacts the CEO with longer hours, job insecurity, shareholder pushback, and bonus reductions.

How user-centred design is reshaping cybersecurity
Tue, 12th Nov 2019
#
devops
#
martech
#
multi-cloud
A user-centered design approach starts with users and asking them what they want to gain a deeper understanding of their needs.

Forcepoint increases cloud security presence to cover 128 countries
Thu, 17th Oct 2019
#
endpoint protection
#
cloud security
#
casb
This PoP expansion brings Forcepoint services to virtually anywhere in the world while delivering optimal security and productivity enhancing capabilities.

Fortune 500 companies failing to demonstrate cybersecurity commitment - Bitglass
Thu, 3rd Oct 2019
#
casb
#
report
#
bitglass
A Bitglass report reveals that 77% of Fortune 500 companies lack transparency in cybersecurity roles, with just 62% having a Chief Information Security Officer.
General staff don't get tech jargon - expert says time to ditch it
Thu, 16th May 2019
#
phishing
#
email security
#
cybersecurity
There's a serious gap between IT pros and general staff, and this expert says it's on the people in IT to bridge it.

Security professionals want to return fire – Venafi
Wed, 20th Mar 2019
#
devops
#
apm
#
software development
Seventy-two percent of professionals surveyed believe nation-states have the right to 'hack back' cybercriminals.

How business leaders must prioritise cyber risk - Palo Alto Networks
Wed, 13th Mar 2019
#
firewalls
#
network infrastructure
#
network security
Prioritising threats ensures organisations are taking a logical approach to cybersecurity, focusing their time and money on the most pressing dangers.

How protecting critical infrastructure starts with securing social media
Tue, 1st Jan 2019
#
iam
#
cybersecurity
#
passwords
Erroneous alerts regarding potential missile strikes that caused civil disruption in Hawaii and Japan in recent history.

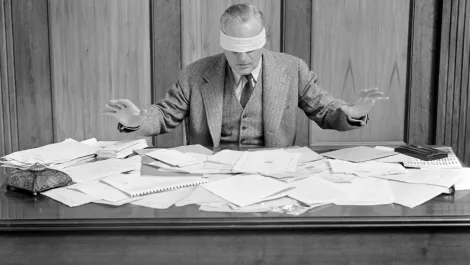
Companies swamped by critical vulnerabilities – Tenable
Fri, 9th Nov 2018
#
report
#
cybersecurity strategy
#
tenable
Research has found enterprises identify 870 unique vulnerabilities on internal systems every day, on average, with over 100 of them being critical.

The key pillars of strong cybersecurity strategies
Fri, 2nd Nov 2018
#
devops
#
multi-cloud
#
iam
A cybersecurity strategy is imperative for a mature security presence in order to improve the chances of surviving current and future cyberattacks.

LogRhythm reports higher-than-anticipated SOAR adoption rate
Thu, 1st Nov 2018
#
siem
#
logrhythm
#
cybersecurity strategy
LogRhythm sees a significant surge as 33% of customers adopt its SOAR capabilities, outpacing Gartner's 2018 SOAR adoption estimates.

More OT devices added to Tenable's industrial security offering
Fri, 19th Oct 2018
#
cybersecurity strategy
#
security week
#
ot
Tenable has expanded its asset discovery and vulnerability management solution to include thousands of new OT devices, enhancing industrial security.

GDPR compliance: Looking beyond the hype
Wed, 17th Oct 2018
#
data protection
#
data privacy
#
opinion
Six months post-GDPR, we demystify compliance myths and provide key insights to navigate the data regulation maze.

Exclusive: Cybersecurity in the API economy
Mon, 15th Oct 2018
#
risk & compliance
#
okta
#
opinion
Application programming interfaces (APIs) are the cornerstone of both connected devices and the connected experience.

Industrial control systems: How to approach OT cybersecurity
Tue, 9th Oct 2018
#
risk & compliance
#
opinion
#
cybersecurity strategy
To secure facilities, operational technology and IT security must come together. PAS Global spoke to industry experts for their strategies.

Carbon Black: Is your cyber panic room ready?
Fri, 5th Oct 2018
#
carbon black
#
opinion
#
cybersecurity strategy
Cybersecurity expert warns of a 'cyber winter' with a surge in destructive attacks, urging digital 'panic rooms'.